A COMPLETE Assessment including a site visit by Certified Cyber Security Specialists. Followed by Role-based training materials. Don’t take risks with online questionnaires.
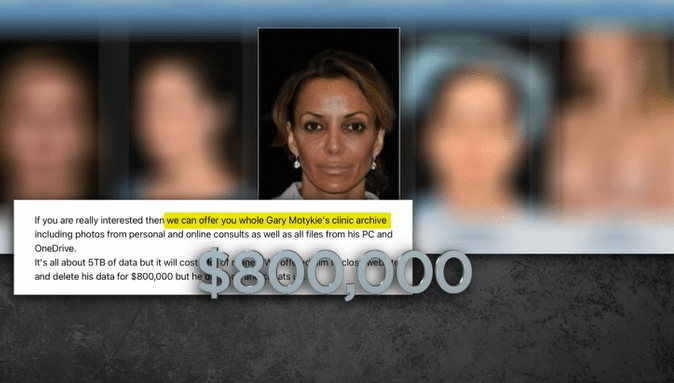
Protecting Patient Data in the Digital Age: The Beverly Hills Plastic Surgeon’s Office Data Breach
Lack of proper data security in healthcare clinic results in loss of trust and reputation In the digital age, data security is a paramount concern, especially in the healthcare industry. Unfortunately, even prominent institutions like Beverly Hills Plastic Surgeon's Office are not immune to the threat of data breaches. Recently, [...]