Common Ways Hackers Get Your Password and How to Stop them
It seems we constantly hear about a data breach of some large corporation in the news. Most data breaches happen due to hackers gaining access to someone’s password. Passwords are the easiest and simplest way to secure an account. Unfortunately, the simplicity is what attracts hackers. They know that they will inevitably find a user with a weak password and be able to gain access to computers on your corporate network. How do hackers get your password you may ask? Below are 5 techniques a hacker uses to obtain passwords.
1) Phishing
No, this isn’t some wacky spelling of fishing. It is one of the more popular ways hackers use to obtain passwords. The way that it works is the hacker will send out an email blast to various users across the internet. Often the email will look like it is from a legitimate website such as a banking website or something to do with Microsoft. Within the phishing email is usually a fraudulent link that when clicked on will ask you to login to “your account”. So, what looks like a legitimate login screen is fake and its sole purpose is to capture the credentials you put in. The best way to protect against this is to use two-factor authentication. That way if the hacker does gain access to your login credentials, they will have another level of security that they will need to get through. Of course, there are ways for hackers to hack two-factor authentication, but it is a good safe guard. The other way to protect against phishing attempts is caution. We should all be more cautious about the links or attachments we click on in an email. If you receive an email that looks suspicious or if you are not certain it is legit it is best to err on the side of caution. Let your IT professional know that you received the email and let them figure out the legitimacy.
2) Password Spraying
This commonly used technique has been a hacker favorite for a while. The way this works is they use scripts and software that is loaded up with all the common passwords such as password, 12345, logmein, etc. So, if the hacker has a list of usernames for an environment, they can just plugin the username and let the password spraying software do the work. The best way to combat this is to use much more secure passwords and try to stay away from the most common ones listed in this article.
3) Credential Stuffing
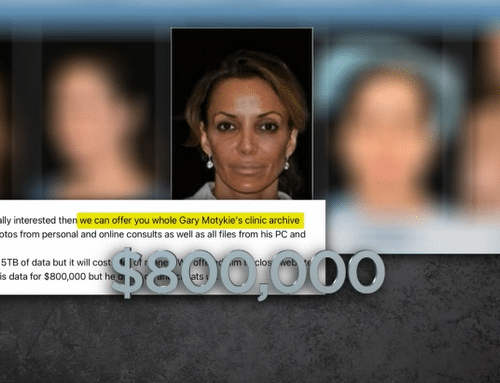
Credential Stuffing is when a hacker uses a database of usernames and passwords that they have obtained by purchasing it on the dark web or directly from another hacker. Usually, when you hear that there was a data breach of a company this is what they are referring to. Say a hacker was able to obtain a login for something like a credit score site. Not much a hacker can do by looking at your credit score but what they can do is use those same login credentials on various websites such as PayPal or banking websites. A lot of times a person will use the same email and password on multiple websites. So, if a hacker has the login credentials for one website there is a high probability, they will be able to use it to gain access to others. The best way to combat this is to never use the same login for multiple websites. I know it is a pain to keep track of all your passwords, but you shouldn’t let that frustration keep you from being less secure. Also, make sure to immediately change your password if you hear of a data breach of a company that may have your login information to access your account with them. If you are curious to see if you have already been compromised, you can use Experian’s dark web scan in this link.
4) Brute Force
This is the method you see depicted in movies and TV shows about hackers. With this method a hacker will use an algorithm to crack an encrypted password. Once the algorithm is run against the account the password is revealed in plain text. This is accomplished by using various hacking tools like Rainbow Crack, John the Ripper, L0phtcrack, etc. These tools perform a dictionary attack which means that the tool will go through the whole dictionary trying each word in a matter of minutes until it finds a password that works. The best way to combat this kind of hack is to make sure that your password isn’t something in the dictionary and is longer than 16 characters with symbols.
5) Key Logging
Key logging is self-explanatory. The hacker will either try to gain access to your computer directly or through some type of spyware that got installed via email or a website. It will then log all the key strokes you make on the keyboard. Using this information, the hacker will compile a list of words typed and use that to run against your accounts. The main way to stop this kind of hack is with good security software that will check for malware, spyware and key logging software.